MCP Registries: Securing Discovery in the Age of Agentic AI
AI Security & Development
AI agents have evolved fast. They now fetch data, execute code, and orchestrate workflows across cloud platforms and APIs. But as they gain more autonomy, one challenge has become impossible to ignore: discovery.
Both humans and agents need reliable ways to find secure servers and tools. For us, discovery is about trust and visibility - knowing that the software we depend on comes from a verified source. For agents, it’s about automation - querying a catalog, validating metadata, and safely connecting to the right system without manual intervention.
Without this layer of assurance, every integration becomes a risk. That’s why MCP registries - catalogs where MCP servers are published, discovered, and vetted - are becoming one of the most important trust layers in the AI ecosystem.
This post is part of my AI Security & Development series. I’ll link to the full, detailed version on Medium.
What MCP Registries Are
Think of an MCP registry like an app store for MCP servers. It is a public or private catalog where developers can publish servers, describe capabilities, and make them discoverable. Instead of digging through GitHub repos or Discord threads, we can query a registry and quickly see:
what the server does
what endpoints it supports
what authentication it uses
what version is running
who maintains it
Today’s ecosystem includes several registry options:
Official MCP Registry (Preview) – positioned as an open, neutral source for discovery
Pulse MCP Directory – tracking more than 6,000 servers
Docker MCP Catalog – over 100 verified containerized servers
GitHub MCP Registry – integrated into Copilot and VS Code
Microsoft MCP Center – enterprise-focused discovery and validation
Community lists – curated examples and collections
Enterprise registries – private catalogs behind policy gateways
This momentum is exciting, but it also reveals fragmentation. Without standards and trust signals, discovery becomes chaotic.
Security and Trust Models
A malicious MCP server is not just another unsafe API request. It can become a direct execution path into systems, data, and workflows. Discovery without security is dangerous.
Key practices emerging in the ecosystem include:
Verified publisher identity and signed releases
Sandboxing metadata that describes execution isolation
Scope transparency and least-privilege defaults
SBOM and CVE visibility
Enterprise gating to enforce internal policy
Registries are not just lists. They are security boundaries that enforce trust before connections occur.
The Lifecycle of an MCP Server
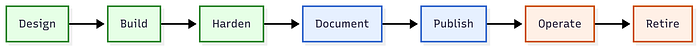
A strong registry supports the entire lifecycle - not just publication.
Lifecycle stages include:
Design – define tools, boundaries, and permissions
Build – implement with SDKs, tests, and SBOMs
Harden – threat model, sandbox, and restrict access
Document – provide metadata and usage guidance
Publish – submit through semantic versioning
Operate – monitor, update, and respond to incidents
Retire – mark deprecated and communicate end-of-life
Without lifecycle discipline, registries become graveyards of abandoned servers.
Opportunities Ahead
The registry ecosystem is still early, but the roadmap is clear:
Better developer experience, including one-click enablement
Private enterprise catalogs with policy enforcement
Marketplaces offering SLAs and compliance levels
Industry-specific bundles based on tags
Observability and quality ratings
Federated registry syncing across providers
Just as app stores accelerated mobile innovation, registries will determine how MCP servers scale beyond early adopters.
What’s Still Missing
Several essential capabilities still lag behind:
Standardized provenance and attestations
Policy languages for install-time enforcement
Richer search and trust UX
Deprecation and lifecycle metadata
Federation standards
These are not optional. They will determine whether registries become reliable infrastructure or fragmentation points.
Practical Takeaways
For engineers: publish with clear metadata, scoped permissions, and SBOMs.
For security teams: favor registries with signing, provenance, and scope visibility.
For enterprises: invest in private registries or gateways to enforce policy.
For vendors: early listings will drive visibility and adoption.
Conclusion: Building the Trust Fabric
In every technology wave, there is a moment when discovery and trust become the real bottleneck. For AI agents, that moment is here.
We have powerful tools. We have thousands of servers. But without a registry layer, we lack the trust fabric needed for safe adoption. And without trust, scale does not happen.
The decisions we make now - around lifecycle, security, and governance - will define how autonomous agents behave in the real world. That’s why MCP registries are becoming a critical piece of the AI security landscape.
Want the full deep dive? Check out my full article on Medium.
🚀 Stay tuned for more posts in AI Security & Development! Follow for more insights on securing AI, cloud, and Web3.
AI Security & Development - AI table of contents included.